TIPS & BEST PRACTICE 01. FEB 2019
Are published email certificates subject to EU GDPR?

In business communications, certificate-based email encryption using S/MIME or OpenPGP is common practice. An employee’s email certificate contains, among other data, their business email address. If a company distributes email addresses according to the [email protected] method, a person’s name and company can be easily identified.
There’s no such thing as a certificate without an email address. After all, it serves to identify you as an in-the-flesh communications partner. Certificates must be publicly available in order to use them for email encryption and signature verification – which is why they are also called public keys, the essence of Public Key Infrastructure (PKI) email encryption. Thus, each user certificate publishes personal data.
What are the legalities of publishing user certificates for email encryption?
The European Data Protection Regulation (EU GDPR) has been in effect since March 2018. However, article 88 regarding data processing in a commercial context has no statutory provisions, rather requires individual countries to enact their own. At the same time, a revised version of the German federal data protection law (BDSG) went into effect. In § 26 par. 1 no. 1 BDSG (revised), there are more concrete regulations concerning data processing in employment circumstances. Still, employee email addresses in business correspondence is not covered.
In comparable cases, in both EU GDPR and BDSG, discussions consider whether exemption from processing is more in the interest of a specific person or whether there are other reasons stringently requiring data processing. When processing is ‘required’ is not clearly defined. There are no categorical statements, neither in legislative texts nor in their justification. We apply our good common sense: certificate publication serves email encryption. Laws such as the EU GDPR require companies to encrypt certain data upon transmission.
We advise companies to include a clause in the employee contracts stating that employee certificates will be published. Employees should then give written confirmation of having read the clause.
Just how public are Z1 Global TrustPoint certificates?
Zertificon operates the online certificate portal Z1 Global TrustPoint. Z1 Global TrustPoint searches public indexes and saves the certificates. Additional certificates come directly over
globaltrustpoint.com or over the publicize function in Z1 SecureMail Gateway.
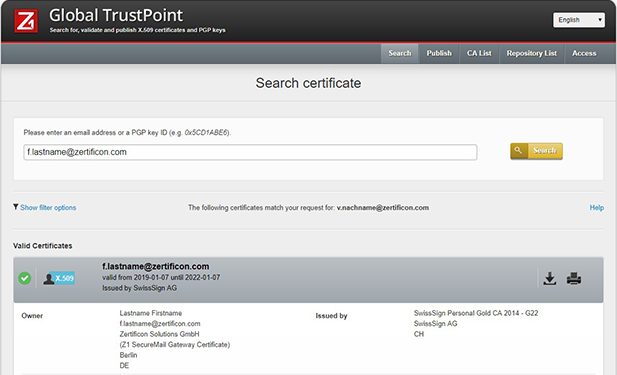
Find public user certificates on Z1 GlobalTrust Point
Nonetheless, Z1 Global TrustPoint is not a public database. Not just anyone can access and download data material. The certificate portal encompasses protective mechanisms that prohibit mass readouts of saved data for address collection. Personal certificates are only displayed upon entering the corresponding email address.
The risk of certificates published via Z1 Global TrustPoint being subjected to unauthorized data gleaning or other privacy infringements is no greater than with email addresses in general. The simple act of sending emails can be targeted and determined whether an email under a certain name exists or not.
Bottom line
We have no hesitations regarding data protection infringements when publicizing certificates on Z1 Global TrustPoint. We do recommend you inform your employees that email certificates are public keys and as such can also be publicly detected.