- Secure Business Email
- Solutions
- Z1 SecureMail Gateway
Z1 SecureMail ONE
Email encryption for Businesses - Plans & Pricing
Overview Z1 SecureMail products Z1 SecureMail Webinars
Introduction
Register now→
Email encryption
with Z1 SecureMail
Duration: < 1 h
- Z1 SecureMail Gateway
Use Cases- EU NIS2 Directive
Email encryption and supply chain security - Email Encryption in the Cloud
Azure / M365, Google Cloud / Workspace - Employment Agencies
S/MIME certificate automation - Email Gateway for Universities
GÉANT TCS certificate management - Secure patient data
Secure GDPR compliant data exchange - Success Stories
- References
Knowledge - Secure File Transfer
- Z1 Energy
- Solutions
- Z1 Energy
Message broker for the energy sector Energy Webinars
Communication
Register now→
in the energy sector
with Z1 Energy
Duration: < 45 min
- Z1 Energy
BenefitsMarket processes - Partner
- Company
- Company
- Support
- Jobs
Z1 SecureMail:
Email encryption
and signing for businesses
Z1 SecureMail automates security, data privacy, and compliance
-
- Encryption & signing according to international standards: S/MIME, OpenPGP, password-based encryption
- Gateway and email certificates from a one-stop shop with affordable certificate prices in a subscription model
- With CertMagic® up to 80% less effort in certificate handling compared to standard gateways on the market
- Professional image with communication partners – automated key exchange also saves effort on your partner’s side
- Competent and renowned Zertificon manufacturer support in German and English
Z1 SecureMail features and pricing
10 or 10,000 users? Find the right plan
How does it work?
Fig. Each email is individually encrypted according to the recipient’s capabilities.
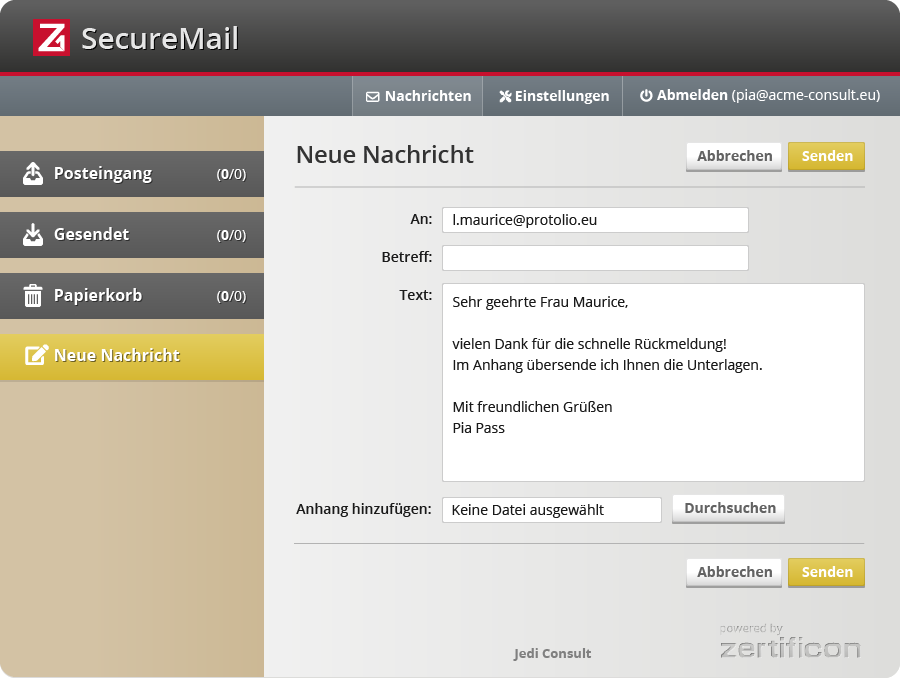
Centralized Automatic
Email Encryption and Signature with a Gateway
Z1 SecureMail Gateway comes as a virtual email encryption appliance which integrates seamlessly into an existing email infrastructure. As an SMTP proxy it processes the entire company-wide email traffic. The Z1 SecureMail Gateway operates as a virtual mail room – processing incoming and preparing outgoing mail. It encrypts and signs outgoing mail whilst decrypting and validating the signature of incoming items. Suspicious emails are automatically blocked and the internal recipient informed. The complete email processing is performed according to ‘Z1 Policies’ which can be fully configured using the web-based administration interface. Z1 SecureMail Gateway works silently and transparently in the background. Sending and receiving emails remains the same for employees.Using the right encryption method:
S/MIME, OpenPGP or password
Video (5 min): Z1 SecureMail sends an email to three contacts simultaneously using different encryption technologies. Security meets efficiency!
Email encryption on-premises, in the cloud, or as SaaS?
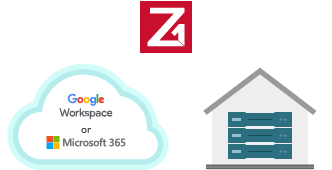
Z1 Virtual Appliance runs on-premises and in the cloud
In your own data center, in the cloud or as a hybrid solution: Z1 SecureMail Gateway is easily and quickly integrated into your existing email infrastructure. Z1 SecureMail is ideally suited for operation with Microsoft 365 and Google Workspace. The anti-spam functions of cloud providers such as Exchange Online Protection (EOP) can be combined with Z1 SecureMail. How email encryption works in the cloud?You receive Z1 SecureMail on a virtual Z1 appliance with a hardened operating system based on Debian Linux.
Supported virtualization environments for the Z1 Virtual Appliance Platform
 |
vSphere ESXI Hypervisor ≥ 6.7 Workstation Pro / Workstation Player ≥ 14.0 |
 |
XenServer Free / Standard / Enterprise Edition ≥ 7.0 |
 |
Windows ≥ 2016 |
 |
Proxmox VE 7.3.x, 7.4.x, 8.1.x |
Email Encryption as a Service
Would you like to operate Z1 SecureMail Gateway as a Software-as-a-Service (SaaS)? We will be happy to put you in touch with one of our MSSP Partners, where you will receive managed services or even email encryption as a fully managed service. If you are interested, please write a short message in the free text field of our request form.
Z1 SecureMail ONE or Z1 SecureMail Gateway
Which solution fits best for me?
Z1 SecureMail ONE |
Z1 SecureMail Gateway |
|
|---|---|---|
| Number of users (mailboxes) | up to 100 | unlimited |
| Purchase process | Buy online | Request an offer |
| Customer service | Customer portal with manuals and ticket support | Consulting as part of the request for quotation, ticket support and service hotline |
| Installation | Self-installation using manuals (ISO file provided as download in the customer portal) | Sales team sends ISO image; optional service available for integration into complex systems |
| Purchase of certificates | Automatic issuance: certificates for all users included in the price | Purchase via Zertificon is optional; type of certificates can be selected |
| Software as a Service | In preparation | Via Zertificon Partners |
| Shared features & benefits |
|
|
Find more details on the features, click here:
Optional Extension: Z1 MyCrypt Outlook Add-In
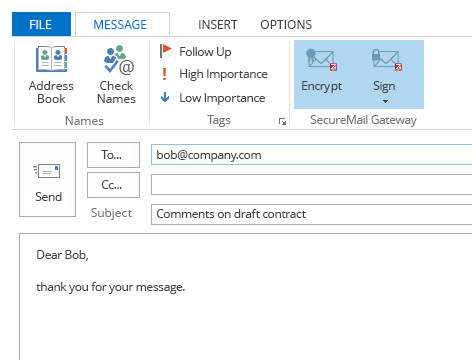
User control through selection of security levels
Create different security levels that your employees can select for each email before sending. For each security level, you assign specific actions such as encryption or signing, which are executed centrally at the gateway. Security and compliance can then be implemented without your employees having to deal directly with encryption tasks.
The client extension for MS Outlook is currently not included in Z1 SecureMail ONE. Z1 MyCrypt is optionally available for Z1 SecureMail Gateway. Z1 MyCrypt can only be used together with a validly licensed Z1 Server product (see service description).
FAQ about Z1 SecureMail
Test and Operation
Test licenses only as part of a PoC
We only issue 30-day test licenses for complex issues and integration challenges as part of a commissioned PoC. Beforehand, all questions must be qualified with us in a consultation. Please contact our sales team via the enquiry form.
Pose your questions in the next live webinar
For all other questions about the operation and integration of Z1 SecureMail, please refer to our live online webinars with product demo.
Our MSSP partners currently provide a SaaS offering. Zertificon itself plans to offer Z1 SecureMail as SaaS in 2025. Register for our newsletter and we will keep you informed of all new developments.
The following technical requirements must be met for the operation of Z1 SecureMail:
for 50 users and average email size of 200 kB
Minimum 8 GB RAM, 2 CPUs, 80 GB storage
- Own mail server, alternatively Microsoft 365 or Google Workspace packages with mail function and PORT 25 sending option.
- Own email domain with access to DNS configuration for domain validation in the certificate reference
- Virtual server with dedicated line to the Internet or fixed IPv4 address, e.g. bookable with Hetzner or IONOS.
The configurations of the packages depend on the load.
for 50 users and average email size of 200 kB
Minimum 8 GB RAM, 2 CPUs, 80 GB storage
Yes, Z1 MyCrypt is the extension for Microsoft Outlook.
Currently only optionally available for Z1 SecureMail Gateway.
Currently only optionally available for Z1 SecureMail Gateway.
Integration
Yes, there is an integration mode for Z1 SecureMail with Microsoft 365 and Google Workspace. The integration is widely used and easy to implement following our instructions.
Our software supports the two most recent versions of the listed virtualization platforms:



Didn’t find your question here? Feel free to use our contact form below.
Contact form for general questions about Z1 SecureMail
For price information or project enquiries, please use the enquiry form.
This is the quickest way to contact sales.